
Threat Modeling AI Systems: A Complete Playbook for Practitioners
The Blast Radius - Edition [4] Over the...

The Blast Radius - Edition [4] Over the...
Mitigating Third-Party Component Risk: Swapping the Cancer for...
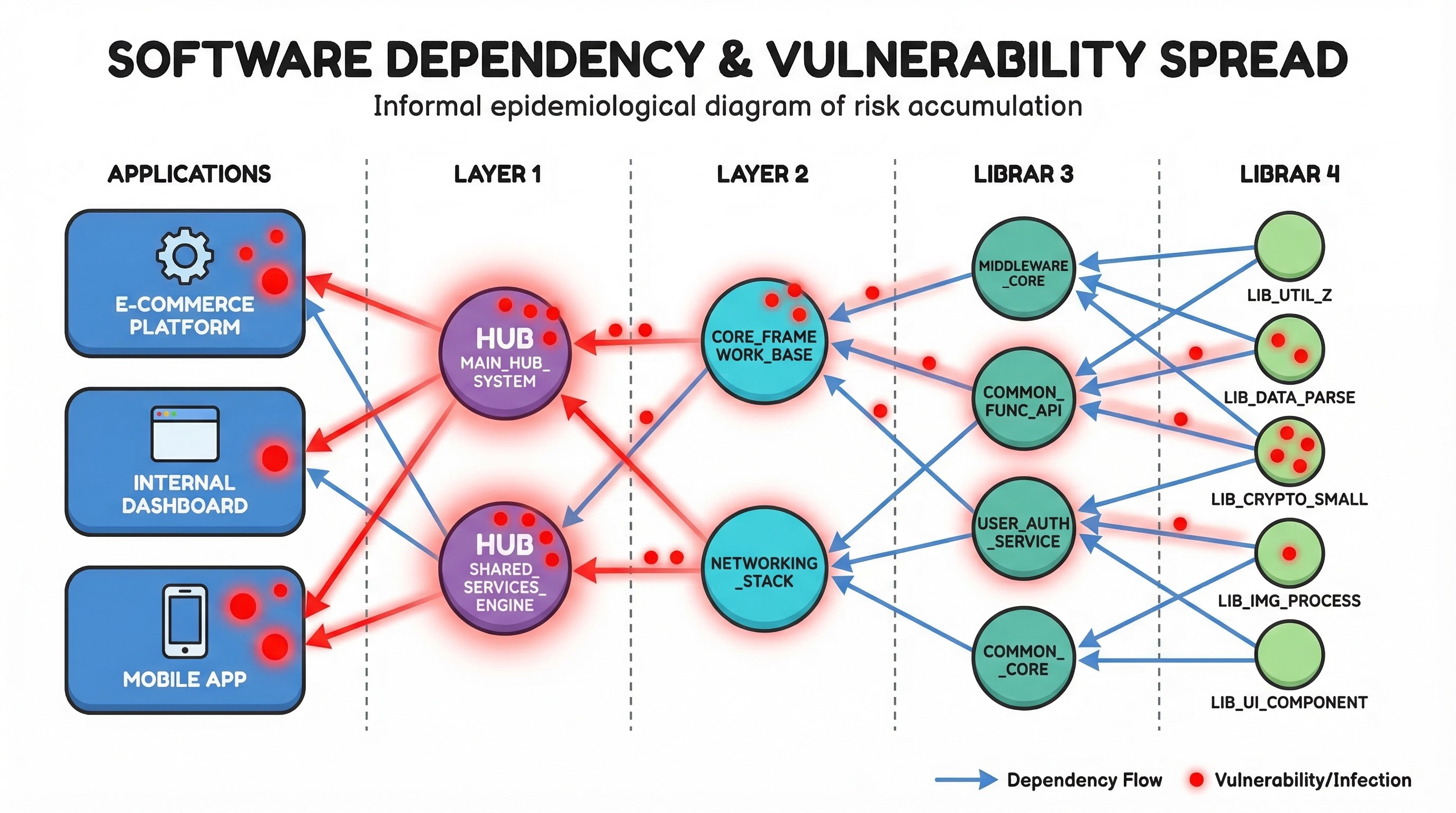
How One Bad Library Can Poison Your Entire...
I’ve been talking about graphs for dependency analysis...

Why are so many people just diving, straight into the code? A minimum of requirements and design? Perhaps a threat Model?
Coming soon to a bookshelf near you, Threat Modeling Gameplay with EoP: A reference manual for spotting threats in software architecture
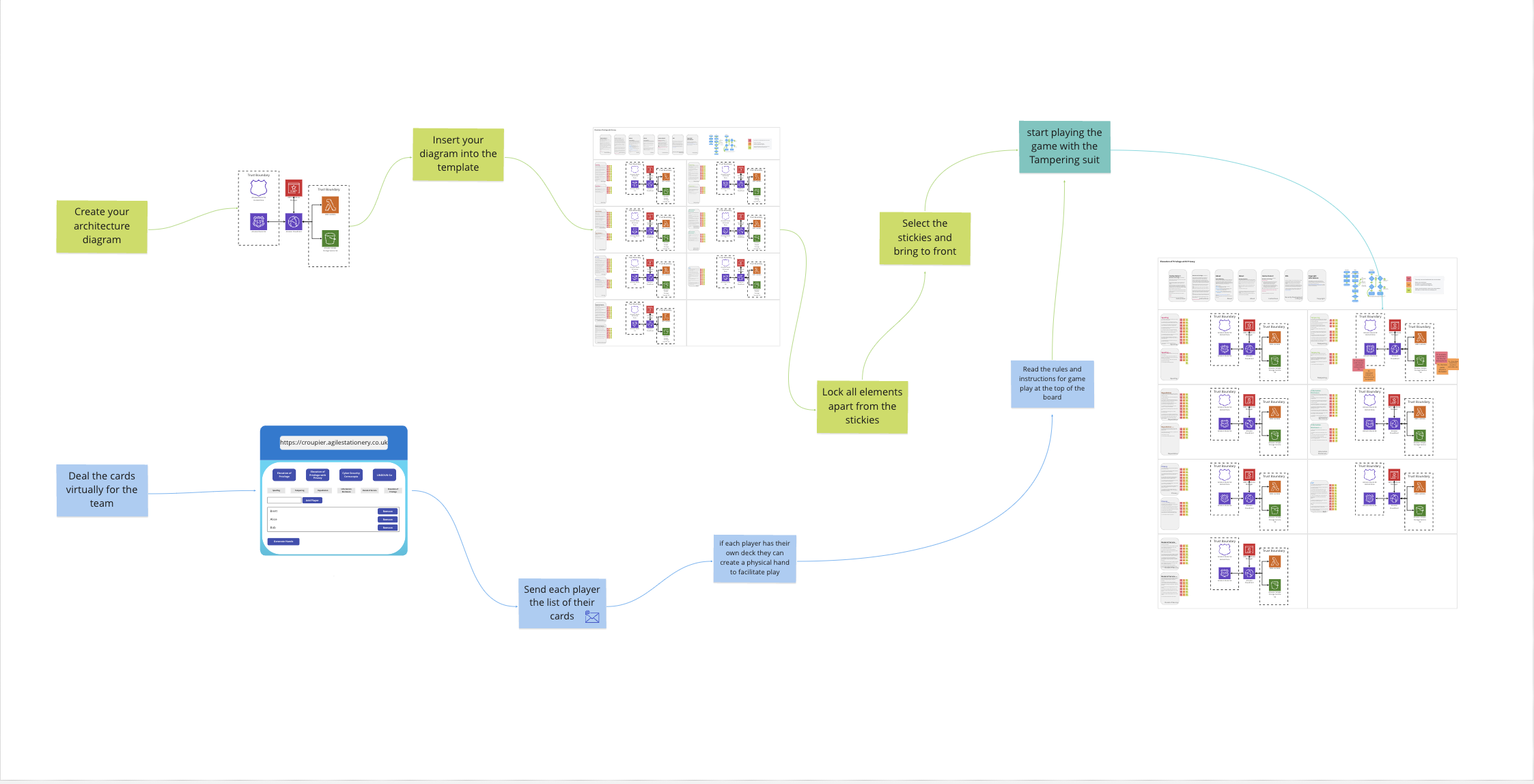
Threat modeling with teams is a process that requires visuals, interaction between team members and discussion and so lends itself to everyone being in a room together. This has been quite hard the last two years. It also doesn’t look to be getting any easier, so we should probably get used to it. Here’s how I’ve been doing it with several teams.
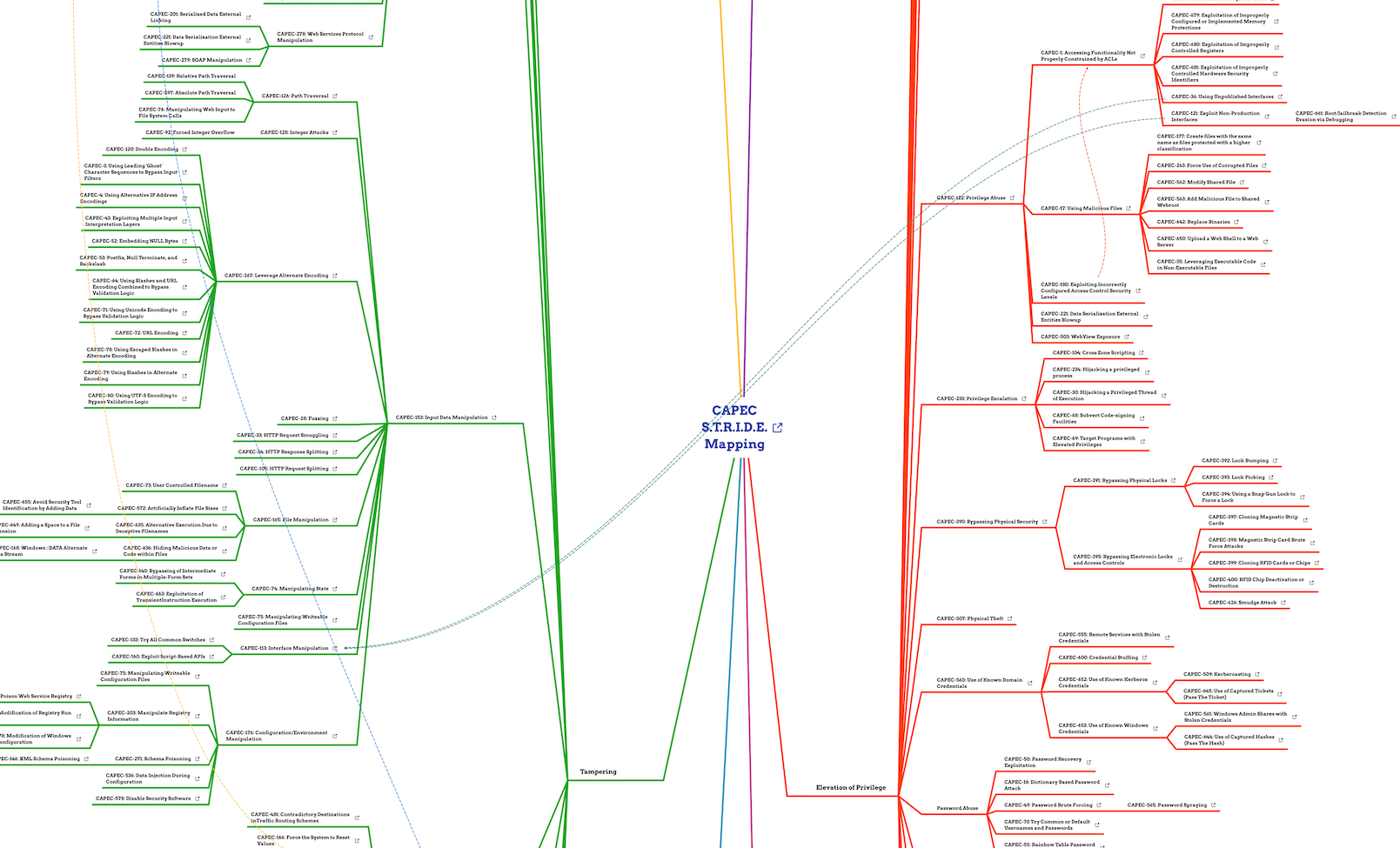
Mapping between the Common Attack Pattern Enumeration and Classification (CAPEC) from Mitre and the S.T.R.I.D.E. Categories used in Threat Modeling.