
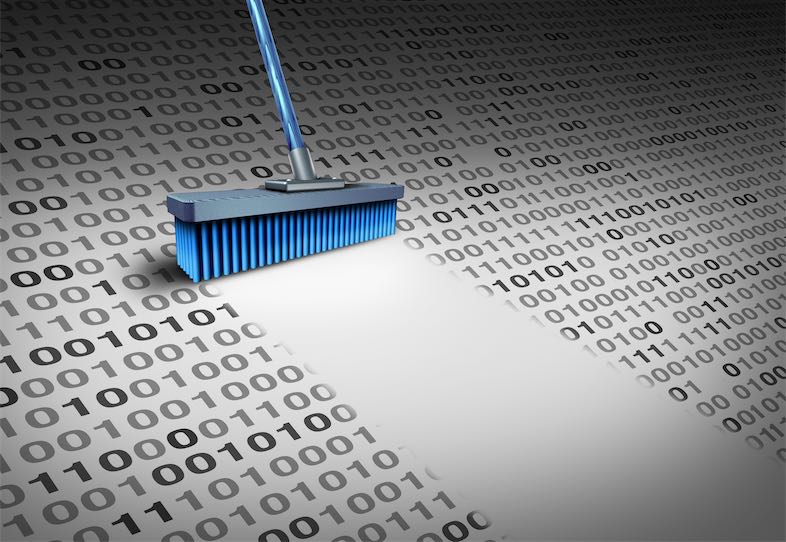
Dependency Pruning and Tree Shaking
Cutting the Dead Wood from Your Dependency Graph...

Cutting the Dead Wood from Your Dependency Graph...
Mitigating Third-Party Component Risk: Swapping the Cancer for...
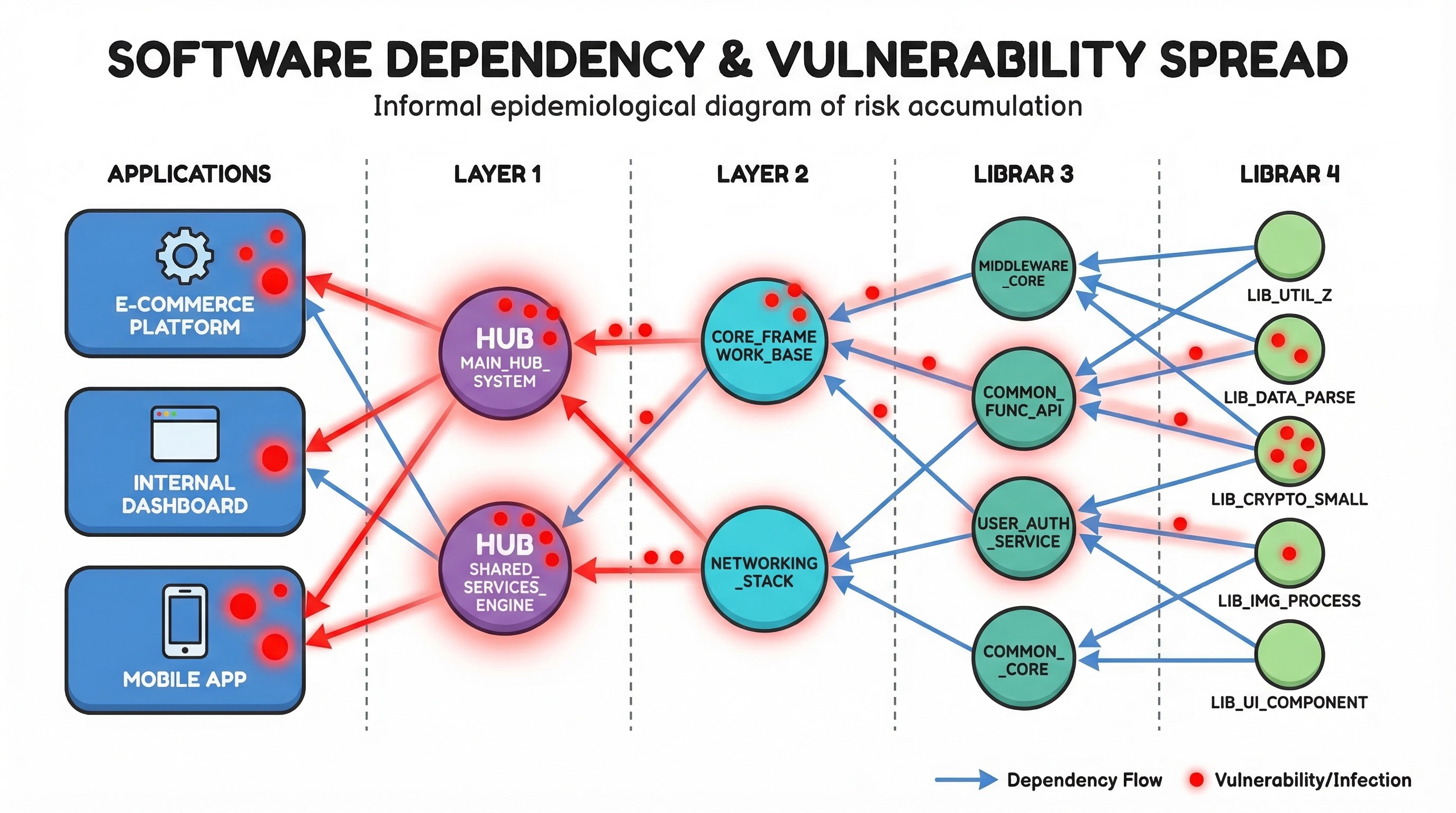
How One Bad Library Can Poison Your Entire...
I’ve been talking about graphs for dependency analysis...
Prioritising remediation of vulnerabilities based on effective impact and risk using PageRank.