
Threat Modeling AI Systems: A Complete Playbook for Practitioners
The Blast Radius - Edition [4] Over the...

Brett is a Seasoned Application Security Engineer and Thought Leader with a Proven Track Record in Software Engineering and Security Best Practices.
Brett has over 10 years of application security experience and 25 years in software engineering. He holds (ISC)² certifications including CISSP, CSSLP, and CCSP. As the author of Threat Modeling Gameplay with EoP and the project lead for the OWASP Application Security Awareness Campaigns, Brett actively contributes to the security community. He also maintains the Ostering.com blog, where he shares insights on security practices.
Brett has successfully collaborated with teams to define security best practices and integrate security by design into their software development lifecycle (SDLC). His training initiatives in threat modeling have led to significant improvements in design quality and security awareness within organizations.
In his spare time, Brett enjoys sports, gardening, cooking, and photography. He is fluent in both English and Italian and holds dual citizenship.
Key Skills: Secure by Design, Privacy by Design, Threat Modeling (STRIDE, EoP, Privacy, LinddunGO, Plot4AI), Secure Coding, Vulnerability Management, and more.
Brett welcomes connections and opportunities to collaborate on innovative security solutions.

The Blast Radius - Edition [4] Over the...
Last week, Anthropic announced Claude Mythos Preview and...
Bear with me on this train of thought....

Cutting the Dead Wood from Your Dependency Graph...
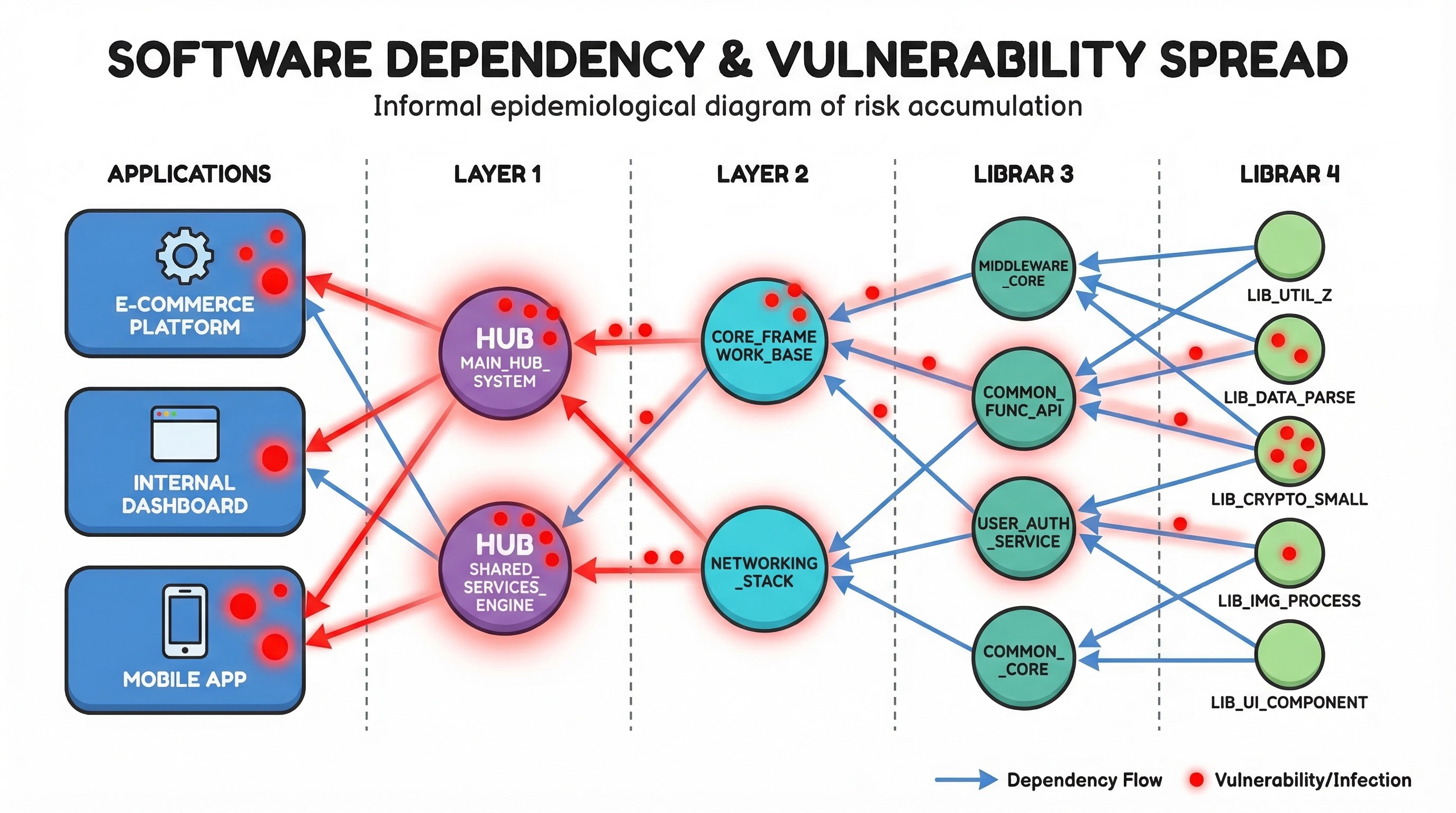
Mitigating Third-Party Component Risk: Swapping the Cancer for...
How One Bad Library Can Poison Your Entire...
I’ve been talking about graphs for dependency analysis...
Why SAST is broken, and how it could...

Cursor as your Secure Dev Team What I...

Building an AppSec Program: A Collaborative Approach Are...
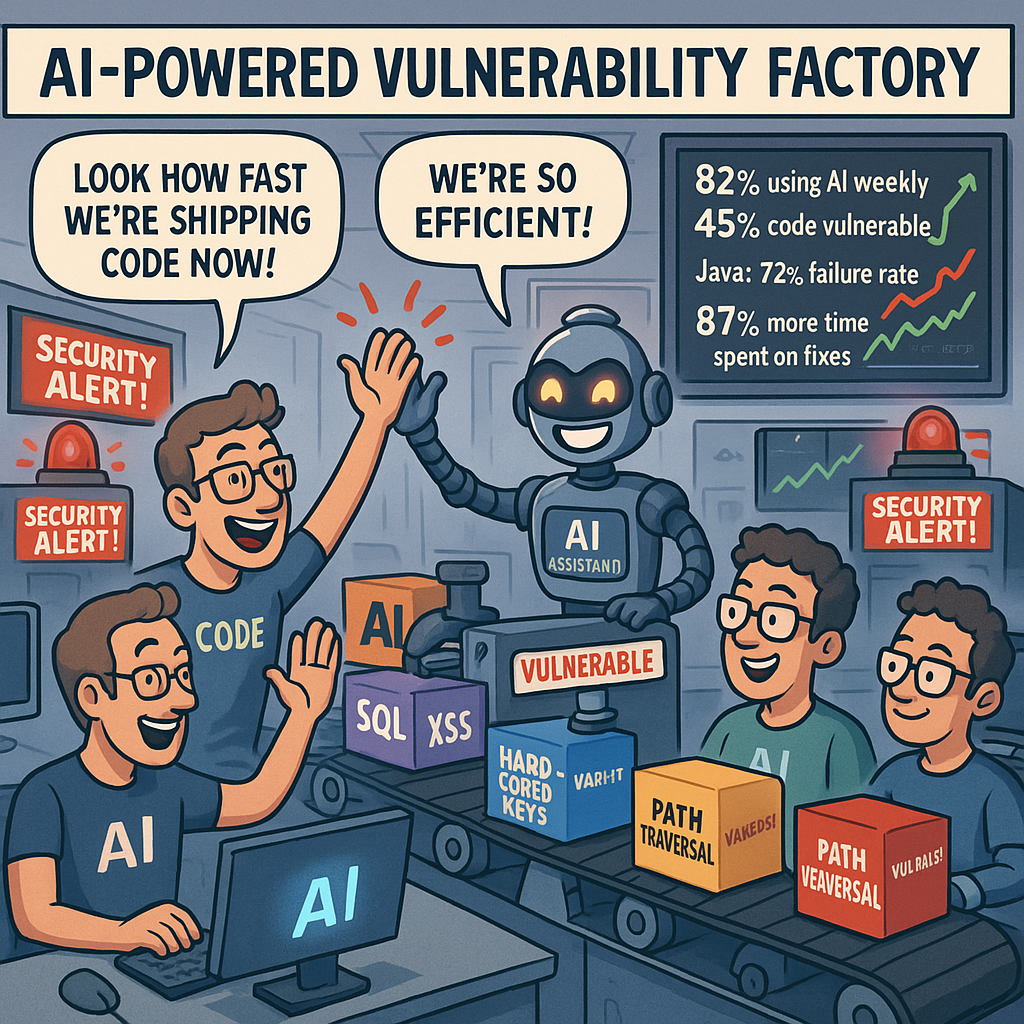
AI-Generated Code: Productivity Gains, Security Pains, and the...

There are lots of ways we can optimise what we do, through a data driven approach, but we need to be careful and use critical and creative thinking.

Why are so many people just diving, straight into the code? A minimum of requirements and design? Perhaps a threat Model?
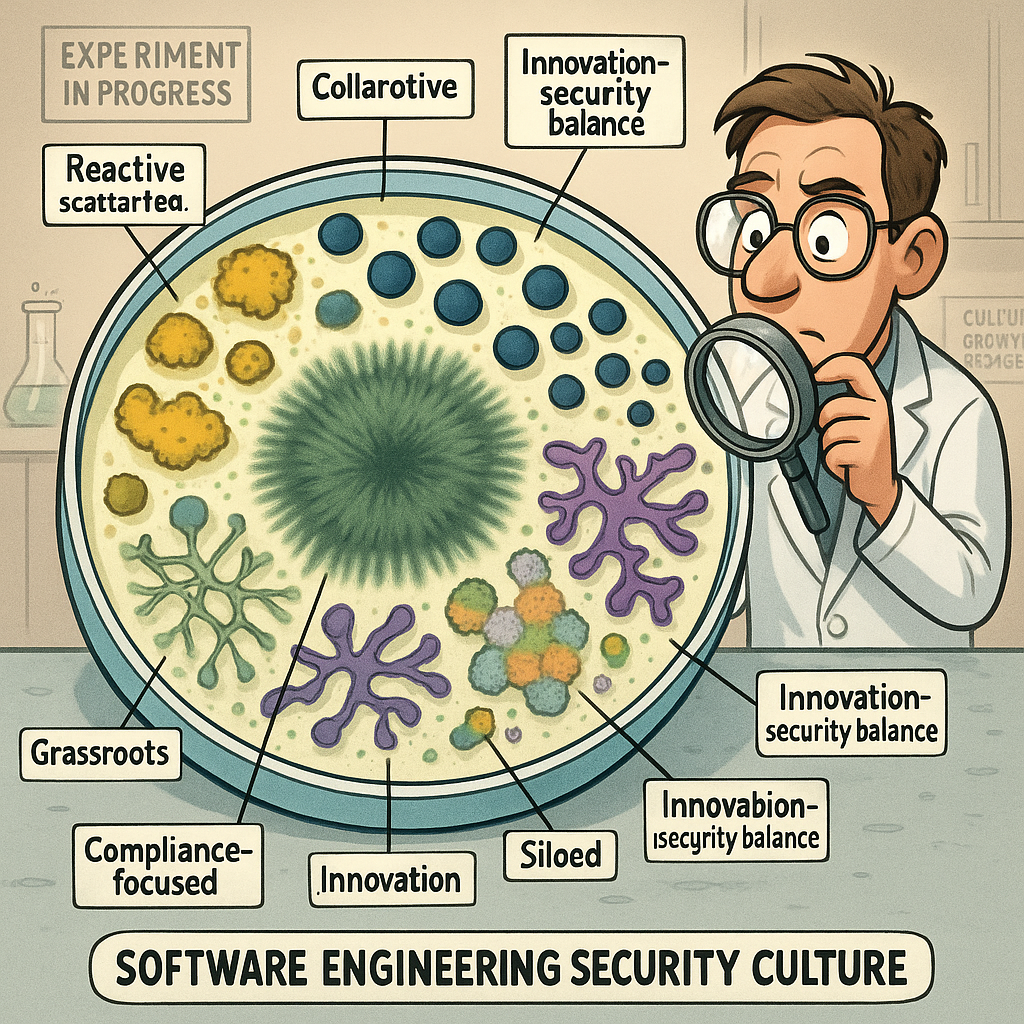
We need to fix the culture, from top to bottom in the software engineering industry. Here are just some of the issues as I see them and what we should be doing about them.
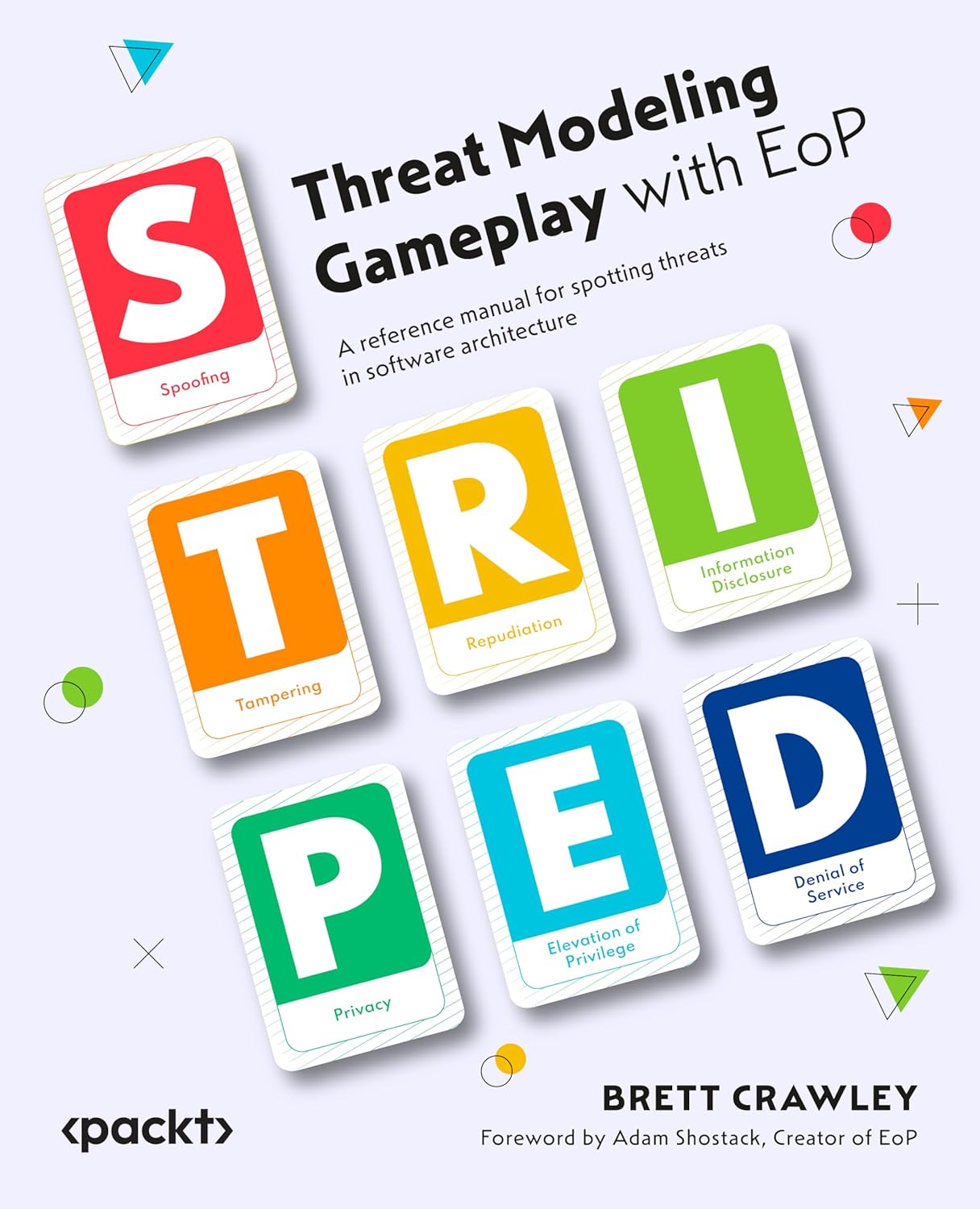
Coming soon to a bookshelf near you, Threat Modeling Gameplay with EoP: A reference manual for spotting threats in software architecture

Some interesting security and creativity games plus a few more